Resolv Protocol suffered a critical smart contract exploit in which an attacker minted approximately $50 million worth of USR stablecoin for roughly $100,000 in USDC a ~500x overcredit. The attacker subsequently converted the minted USR into ETH across multiple DEX venues, extracting an estimated $25 million or more before the protocol team paused all functions. This report details the root cause, attack mechanics, exit strategy, and key takeaways.
Incident Overview
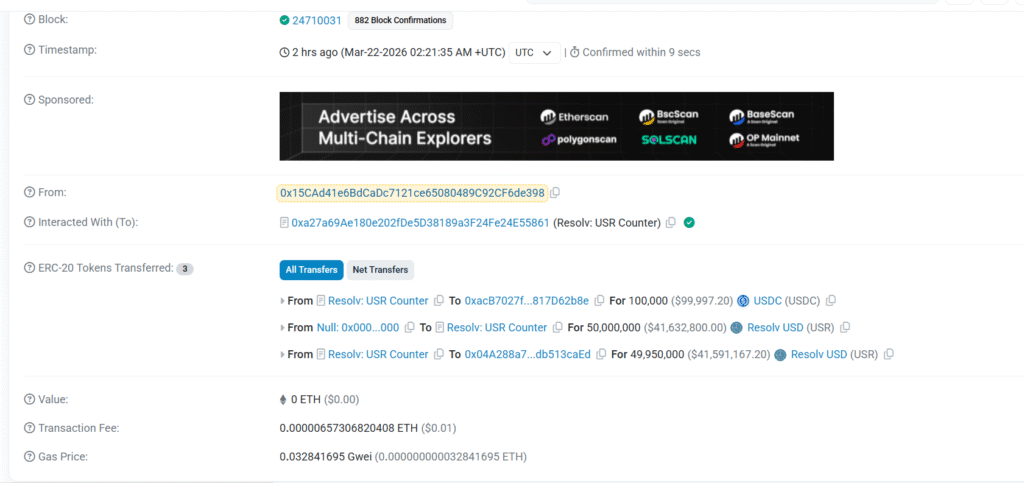
At 2:21 AM UTC, Resolv’s USR Counter contract was exploited. The attacker deposited 100,000 USDC into the contract and received approximately 49,950,000 USR in return — tokens backed by nothing representing a catastrophic failure in the minting validation logic. Prior to the pause, Resolv held over $500 million in total value locked (TVL).
Root Cause
The exploit originated in the requestSwap → completeSwap two-step asynchronous minting flow within Resolv’s USR Counter contract. The _targetAmount field encoded in the transaction’s input data read:
50,000,000,000,000,000,000,000,000 (i.e., 50 million × 10¹⁸)
This inflated value was accepted and fulfilled by the service role a standard externally owned account (EOA), not a multisig without any on-chain validation of the requested mint amount. Critically, neither the Counter contract nor the SimpleToken contract implemented oracle-based sanity checks, upper-bound mint limits, or amount consistency validation between the request and completion steps.
The service role simply completed whatever swap amount was requested. There was no guardian between intent and execution.
The three most probable failure vectors, in order of likelihood:
- Missing amount validation between requestSwap and completeSwap the contract trusted the caller-supplied amount unconditionally.
- Compromised or manipulated off-chain signer the service role EOA may have been tricked or compromised into signing the inflated completion.
- Oracle manipulation though less likely given the simplicity of the exploit, a gamed price feed could have produced the inflated output.
On-Chain Attack Sequence
The exploit unfolded in three clean phases:
Phase 1 — Mint 100,000 USDC was deposited into Resolv’s USR Counter contract (0xa27a…5861) via requestSwap. The completeSwap was subsequently fulfilled, minting 50,000,000 USR from the null address directly to the Counter. 49,950,000 USR was then forwarded to the attacker’s address (0x04A288a7…caEd), while the original 100,000 USDC was routed to an intermediary address (0xacB7027f…2b8e).
Confirmed on-chain transactions: $50M mint: 0xfe37f25e…33743 $30M mint: 0x41b6b937…1f18f
Phase 2 — Wrap and Dump The attacker converted USR into wstUSR to access deeper DEX liquidity pools:
- 20M USR → 17.65M wstUSR
- 15M USR → 13.24M wstUSR
wstUSR was then liquidated across multiple venues in rapid succession:
- 8.77M wstUSR → 9.7M USDT (KyberSwap)
- 2M wstUSR → 2.01M USDC (direct contract)
- 1.31M wstUSR → 655K USDT (KyberSwap)
- 1.31M wstUSR → 148K USDT (KyberSwap — heavy slippage)
- 604K wstUSR → 568K USDT
- 300K wstUSR → 277K USDC (Velora)
- 300K wstUSR → 303K USDC (Velora)
- Dozens of 100K–150K wstUSR clips through Velora at deteriorating rates
wstUSR was selling at $0.50–$0.88 on the dollar across different trades, with slippage worsening as liquidity drained. Multiple failed transactions were visible on-chain, indicating urgency and pace.
Phase 3 — Stables to ETH The attacker aggressively converted accumulated stablecoins into ETH to obscure and preserve value:
- 4.85M USDT → 2,297 ETH (contract 0xbeef…c555)
- 1.66M USDT → 789 ETH (Uniswap V4)
- 2.02M USDC → 948 ETH (MetaMask Swaps)
- 1.5M USDT → 703 ETH (MetaMask Swaps)
- 2M USDT → 938 ETH (MetaMask Swaps)
- 808K USDT → 384 ETH
- 760K USDT → 362 ETH
- 656K USDT → 312 ETH
- 370K USDT → 174 ETH
Notably, multi-million dollar swap legs were routed through MetaMask Swaps an unusual choice that may reflect an attempt to fragment the trail across routing interfaces. The attacker was still actively unwinding remaining wstUSR positions at the time of reporting.
Estimated Impact
| Category | Value |
|---|---|
| USR minted (unbacked) | ~$50 million |
| Estimated extraction | $25 million+ |
| Protocol TVL at time of exploit | $500 million+ |
| Attacker’s initial capital | ~$100,000 USDC |
| Leverage achieved | ~500x |
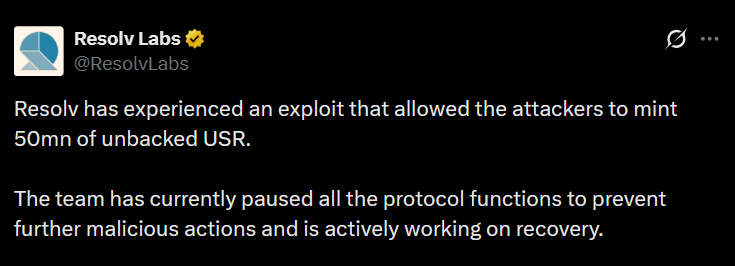
Protocol Response
The Resolv team identified the exploit and paused all protocol functions to prevent further malicious minting or withdrawals. The team has confirmed awareness of the unbacked USR minted and stated they are actively working on recovery. No further detail on remediation or compensation has been published at the time of this report.
Key Failures and Lessons
The Resolv exploit is a case study in what happens when privilege is concentrated in a single, unguarded role. Several distinct failures converged:
The service role was an EOA, not a multisig. A single key potentially compromised, potentially phished, potentially manipulated had the power to complete arbitrary-sized mint operations with no second check.
There were no on-chain mint caps or bounds checking. Neither the Counter contract nor the SimpleToken contract validated whether the completion amount was economically reasonable relative to the deposited collateral. A $100K deposit producing $50M in output should have been rejected at the contract level.
The two-step async flow created a trust gap. requestSwap and completeSwap are decoupled, meaning the amount validated at request time was never re-verified at completion. This is a well-known vulnerability pattern in async DeFi architectures.
No oracle check on the output side. Even a simple sanity check does the minted amount correspond to the market value of the deposited collateral within some tolerance would have blocked this.
Disclaimer
This report is based on publicly available on-chain data and community disclosures at the time of writing. Some figures are estimates. The situation may have evolved since initial reporting. This is not financial advice.